Create NAT Gateway
Create NAT Gateway for High Availability
ℹ️ Production Best Practice
For production workloads, deploy NAT Gateways in multiple Availability Zones to eliminate single points of failure and ensure high availability for your private subnet resources.
Create First NAT Gateway
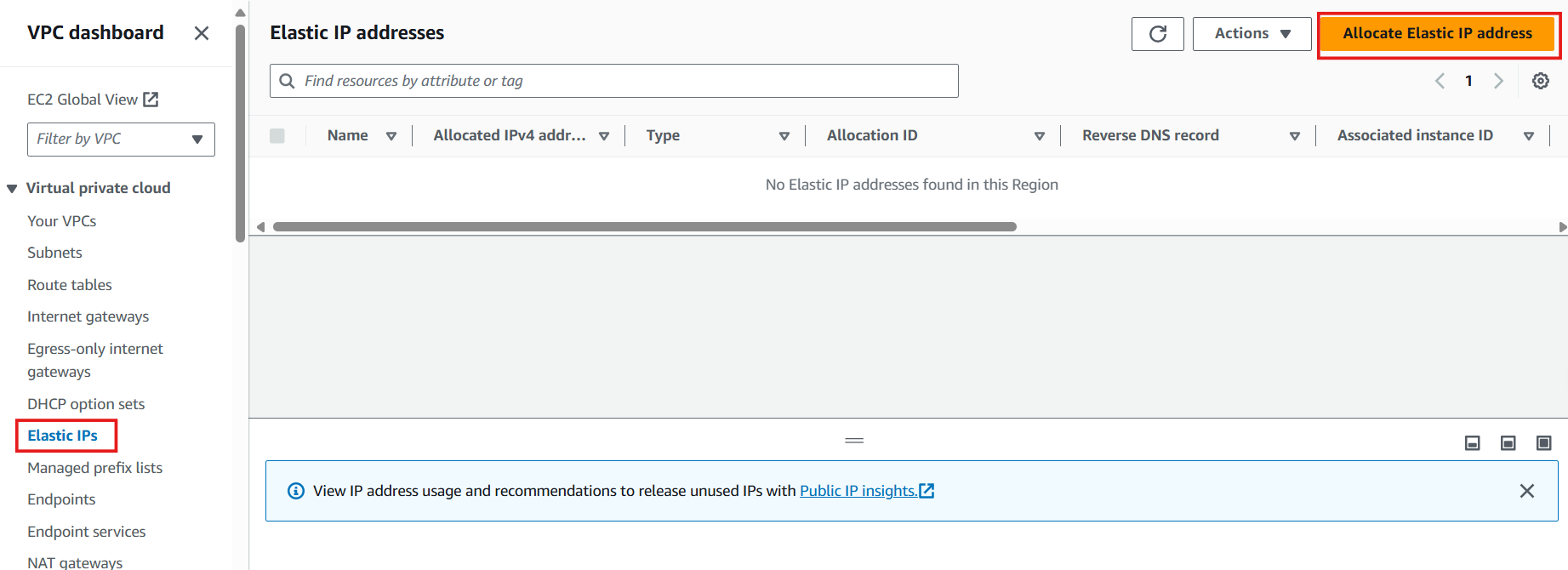
- Access EC2:
- Select Elastic IPs
- Select Allocate Elastic IP address
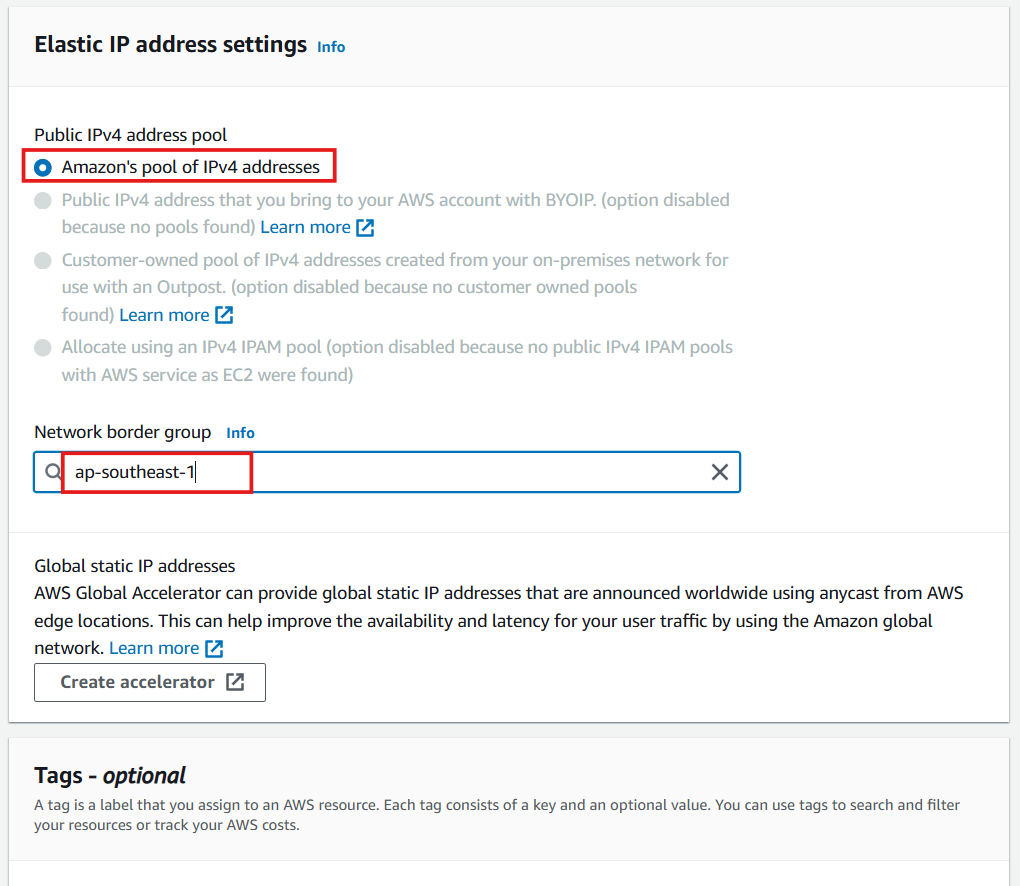
- In the Allocate Elastic IP address interface:
- Public IPv4 address pool: Select Amazon’s pool of IPv4 addresses
- Name tag: Enter
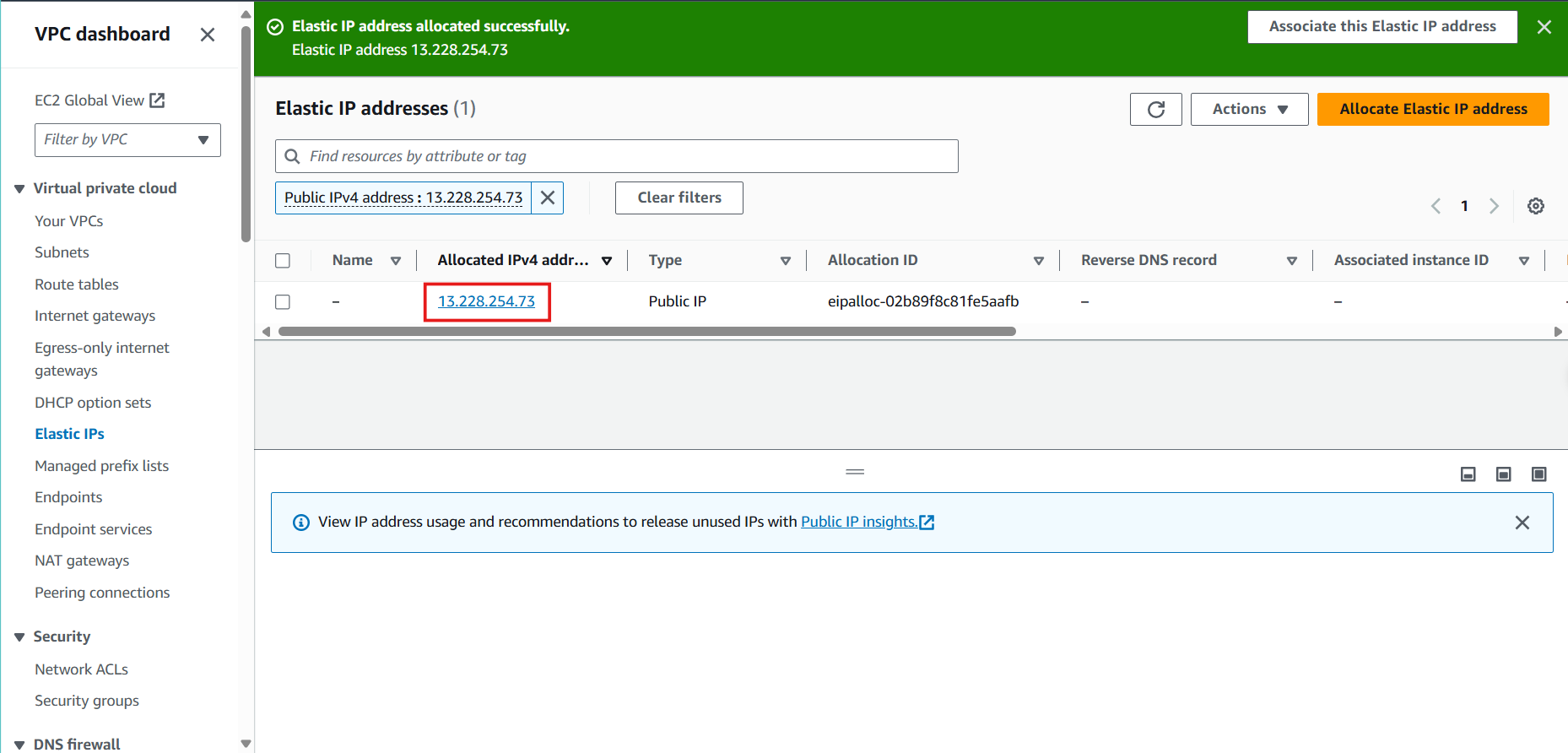
EIP-NAT-AZ1a - Select Allocate
- Create second Elastic IP for high availability:
- Click Allocate Elastic IP address again
- Name tag: Enter
EIP-NAT-AZ1b - Select Allocate
Create NAT Gateways in Multiple AZs
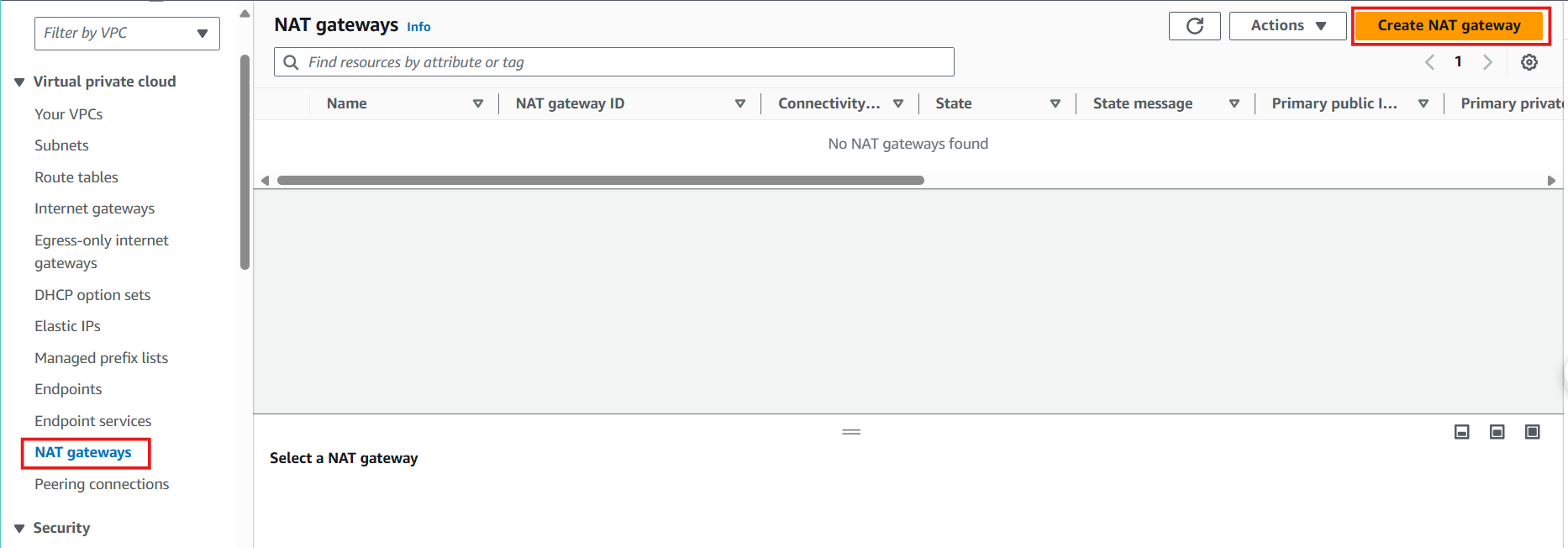
- Access VPC:
- Select NAT Gateways
- Create NAT gateway
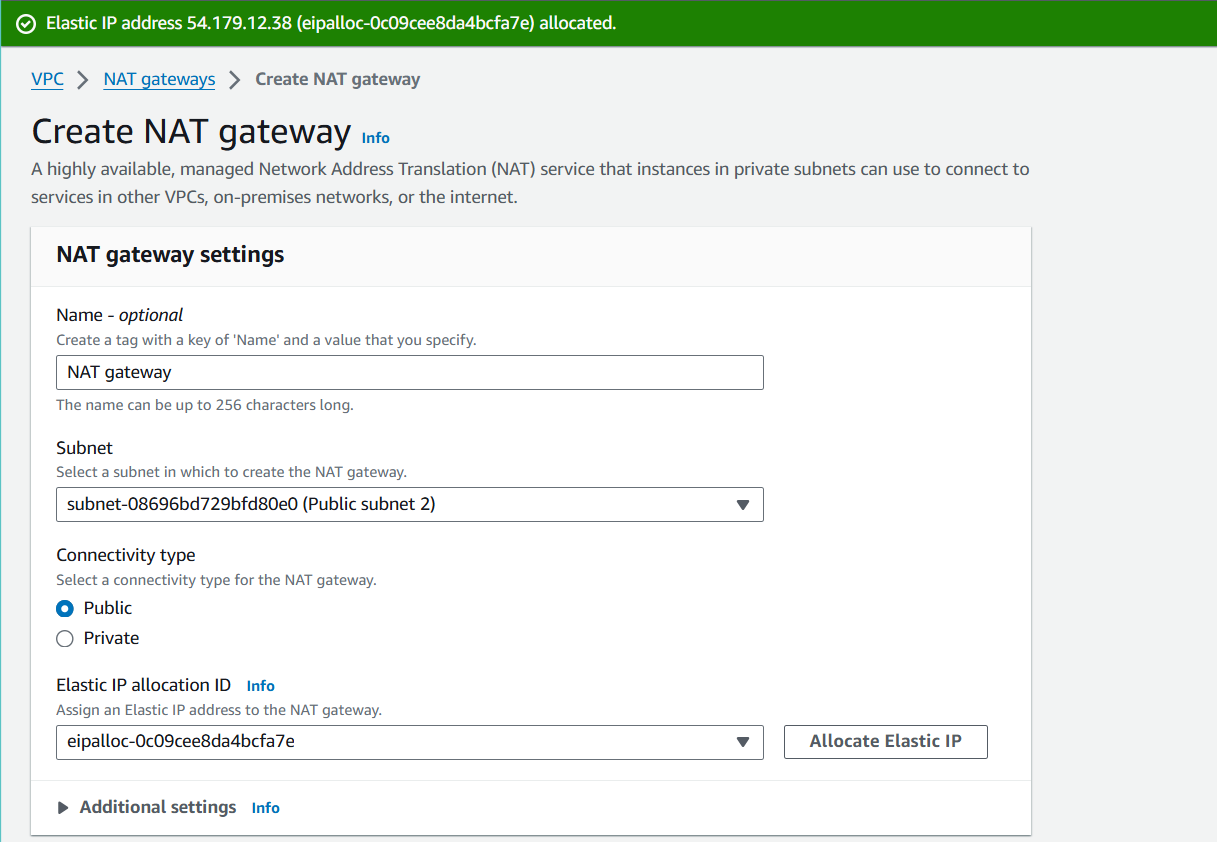
- Configure first NAT Gateway:
- Name: Enter
NAT-Gateway-AZ1a - Subnet: Select Public subnet 1 (ap-southeast-1a)
- Connectivity type: Select Public
- Elastic IP allocation ID: Select EIP-NAT-AZ1a
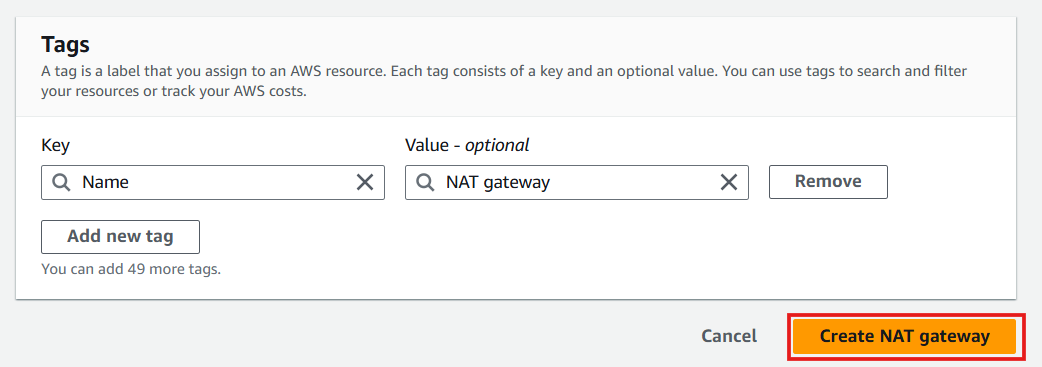
- Click Create NAT gateway
- Name: Enter
- Create second NAT Gateway:
- Click Create NAT gateway again
- Name: Enter
NAT-Gateway-AZ1b - Subnet: Select Public subnet 2 (ap-southeast-1b)
- Connectivity type: Select Public
- Elastic IP allocation ID: Select EIP-NAT-AZ1b
- Click Create NAT gateway
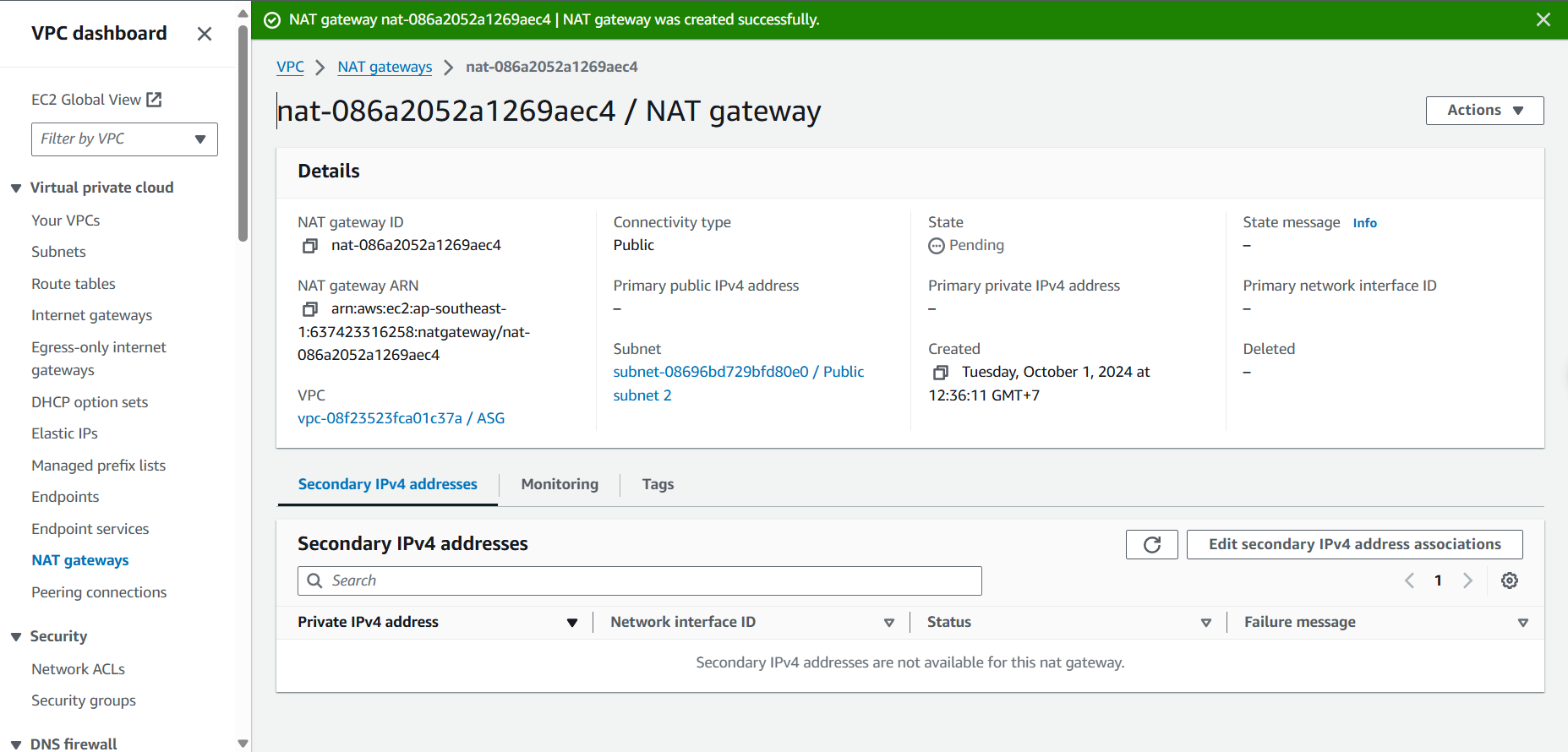
- Verify both NAT Gateways are created:
- Wait for both NAT Gateways to reach Available state
- This ensures high availability across multiple AZs
Create Route Tables for High Availability
Create Route Table for AZ-1a Private Subnets
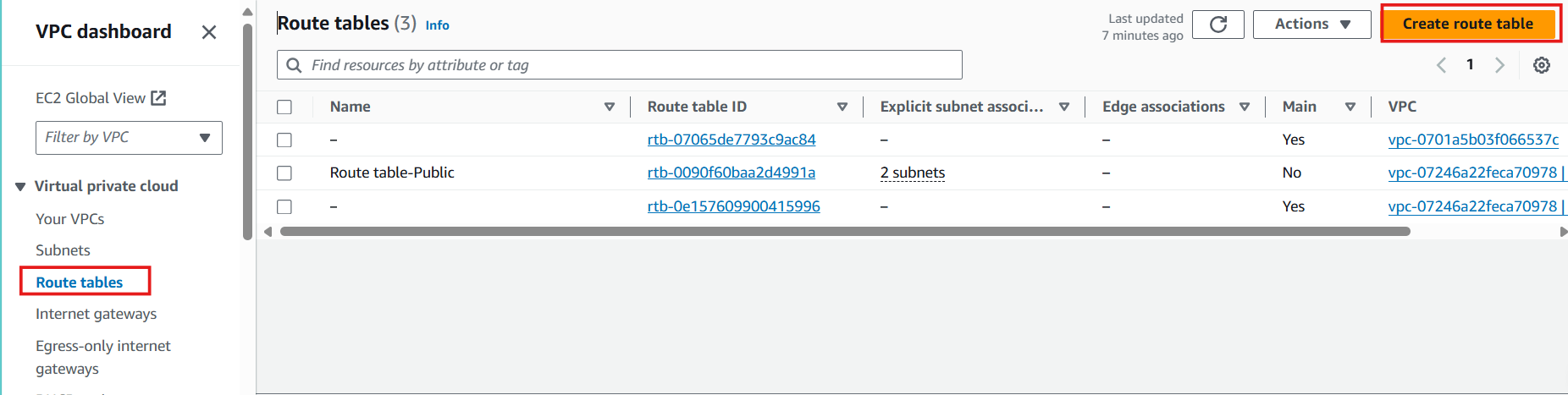
- In the VPC interface:
- Select Route Tables
- Select Create route table
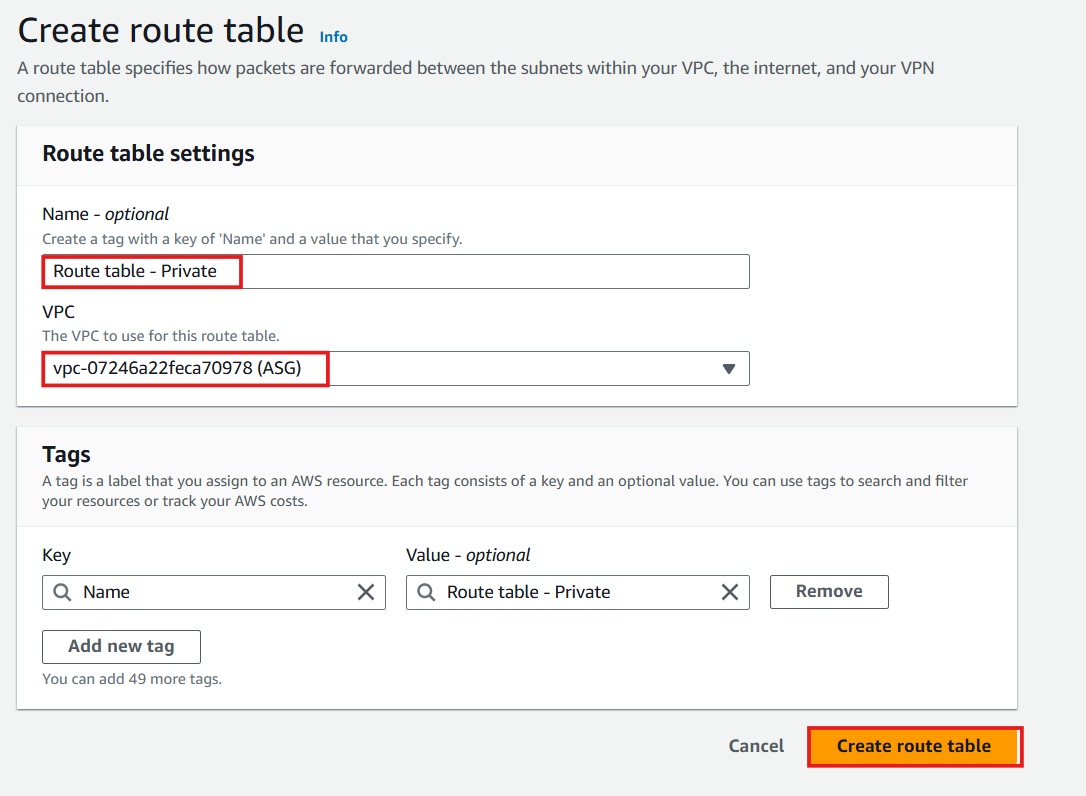
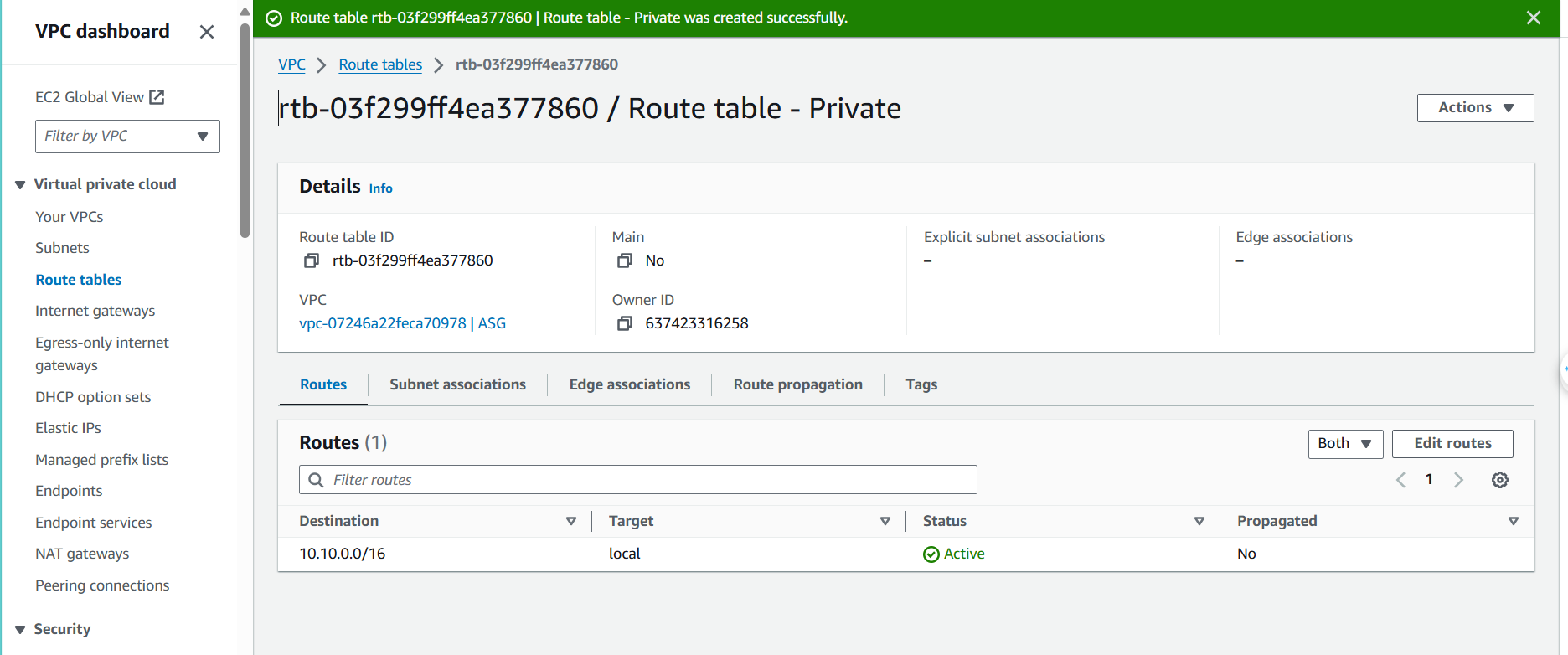
- Configure first private route table:
- Name: Enter
Route-table-Private-AZ1a - VPC: Select ASG VPC
- Select Create route table
- Name: Enter
- Create second private route table:
- Click Create route table again
- Name: Enter
Route-table-Private-AZ1b - VPC: Select ASG VPC
- Select Create route table
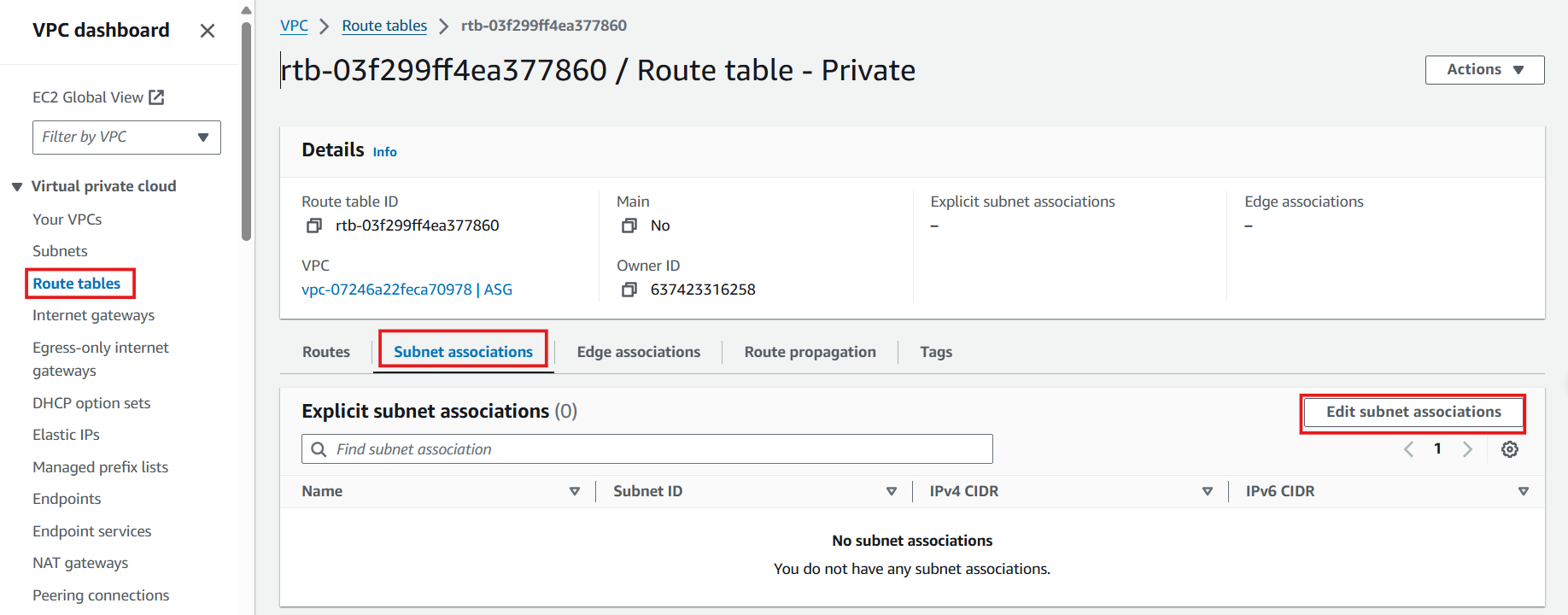
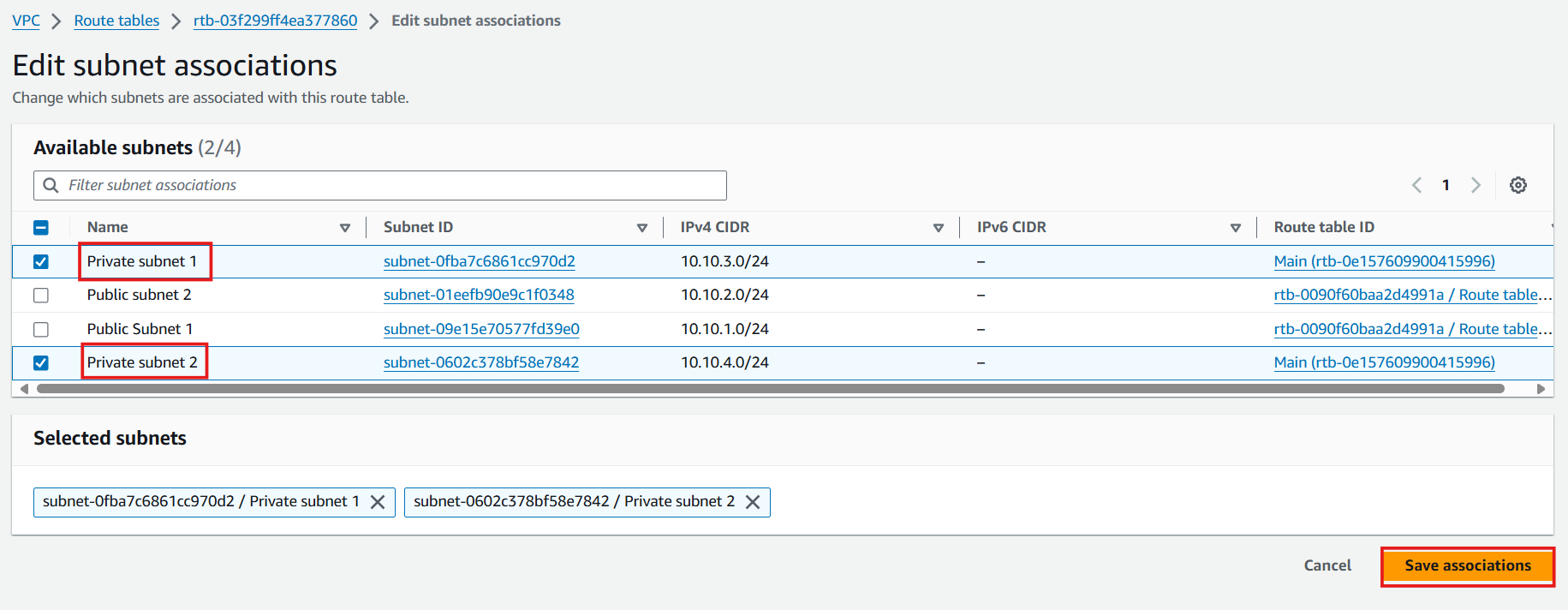
Associate Subnets with AZ-Specific Route Tables
- Configure AZ-1a route table associations:
- Select Route-table-Private-AZ1a
- Select Subnet Associations tab
- Click Edit subnet associations
- Select Private Subnet 1 (ap-southeast-1a)
- Click Save associations
- Configure AZ-1b route table associations:
- Select Route-table-Private-AZ1b
- Select Subnet Associations tab
- Click Edit subnet associations
- Select Private Subnet 2 (ap-southeast-1b)
- Click Save associations
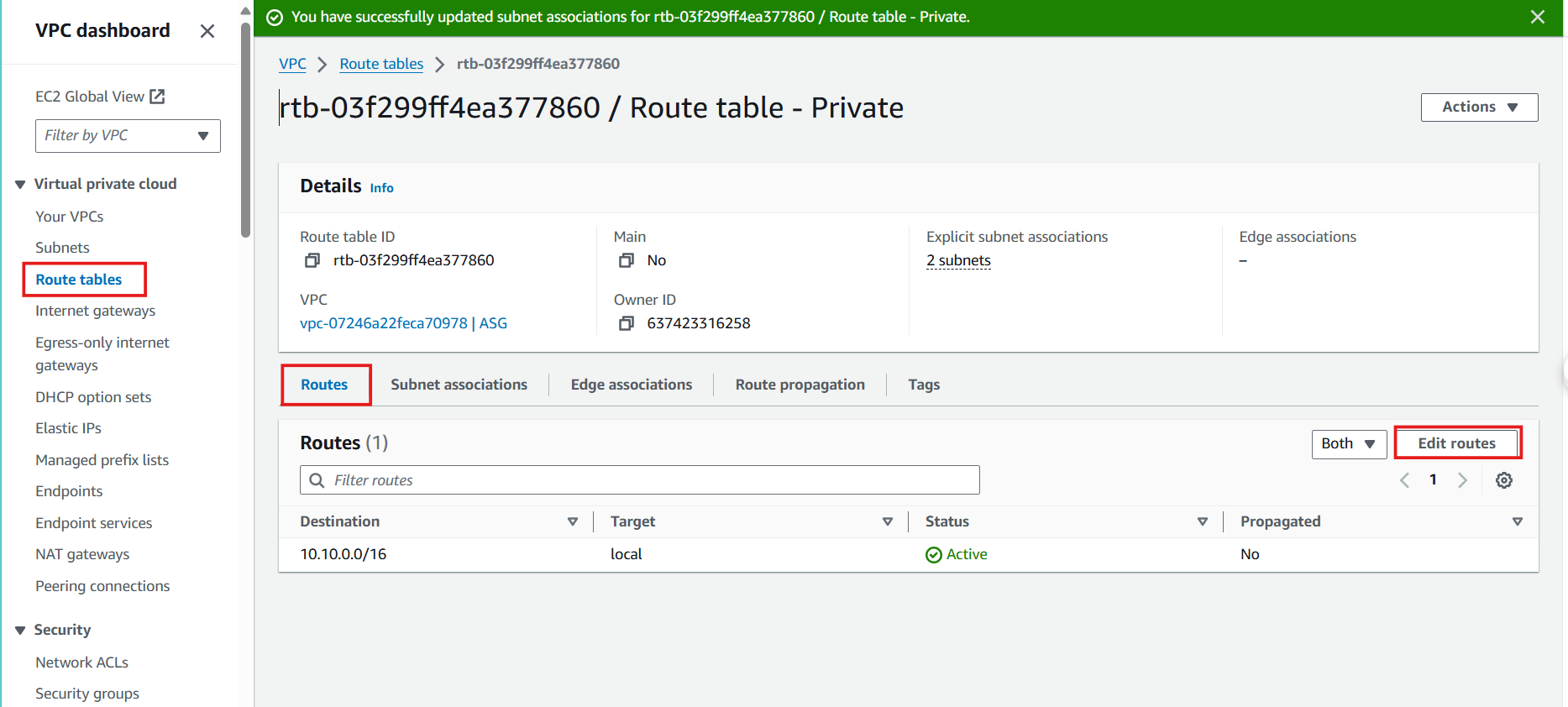
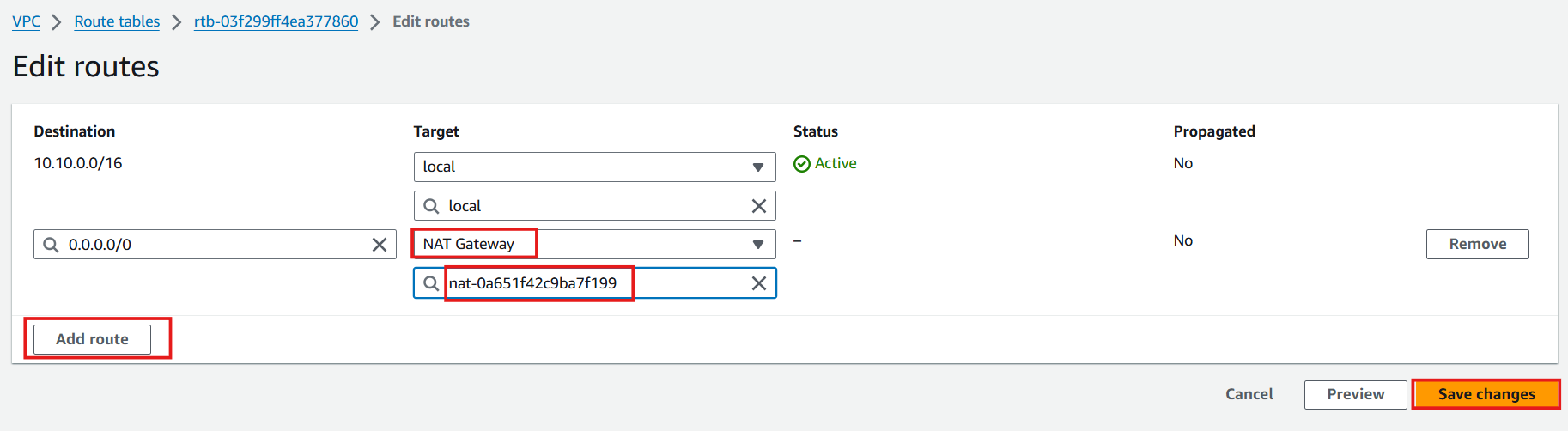
Configure Routes to NAT Gateways
- Configure AZ-1a route to NAT Gateway:
- Select Route-table-Private-AZ1a
- Select Routes tab
- Click Edit routes
- Click Add route
- Destination: 0.0.0.0/0
- Target: Select NAT Gateway and choose NAT-Gateway-AZ1a
- Click Save changes
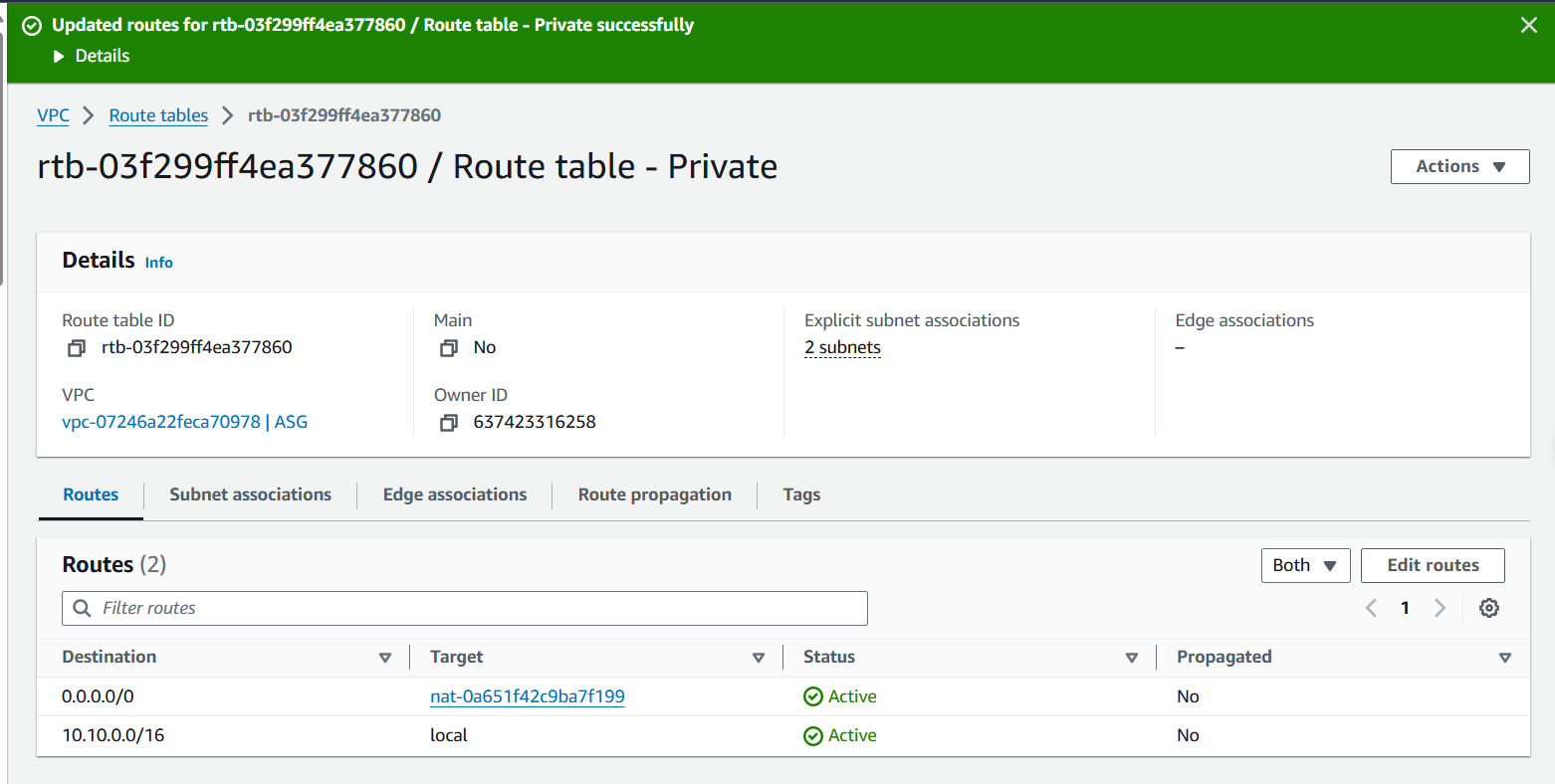
- Configure AZ-1b route to NAT Gateway:
- Select Route-table-Private-AZ1b
- Select Routes tab
- Click Edit routes
- Click Add route
- Destination: 0.0.0.0/0
- Target: Select NAT Gateway and choose NAT-Gateway-AZ1b
- Click Save changes
- Verify route table configurations:
- Each private subnet now routes through its AZ-local NAT Gateway
- This provides fault isolation and optimal performance
🏗️ High Availability Architecture Benefits:
- Fault Tolerance: Failure of one AZ doesn’t affect the other
- Performance: Traffic stays within the same AZ
- Cost Optimization: Reduced cross-AZ data transfer charges
- Scalability: Each NAT Gateway can handle up to 45 Gbps
💰 Cost Considerations:
- Multiple NAT Gateways: Higher hourly costs but better availability
- Data Processing: Each NAT Gateway charges for data processed
- Cross-AZ Traffic: Eliminated by keeping traffic within AZ
- Production Trade-off: Higher cost for better reliability
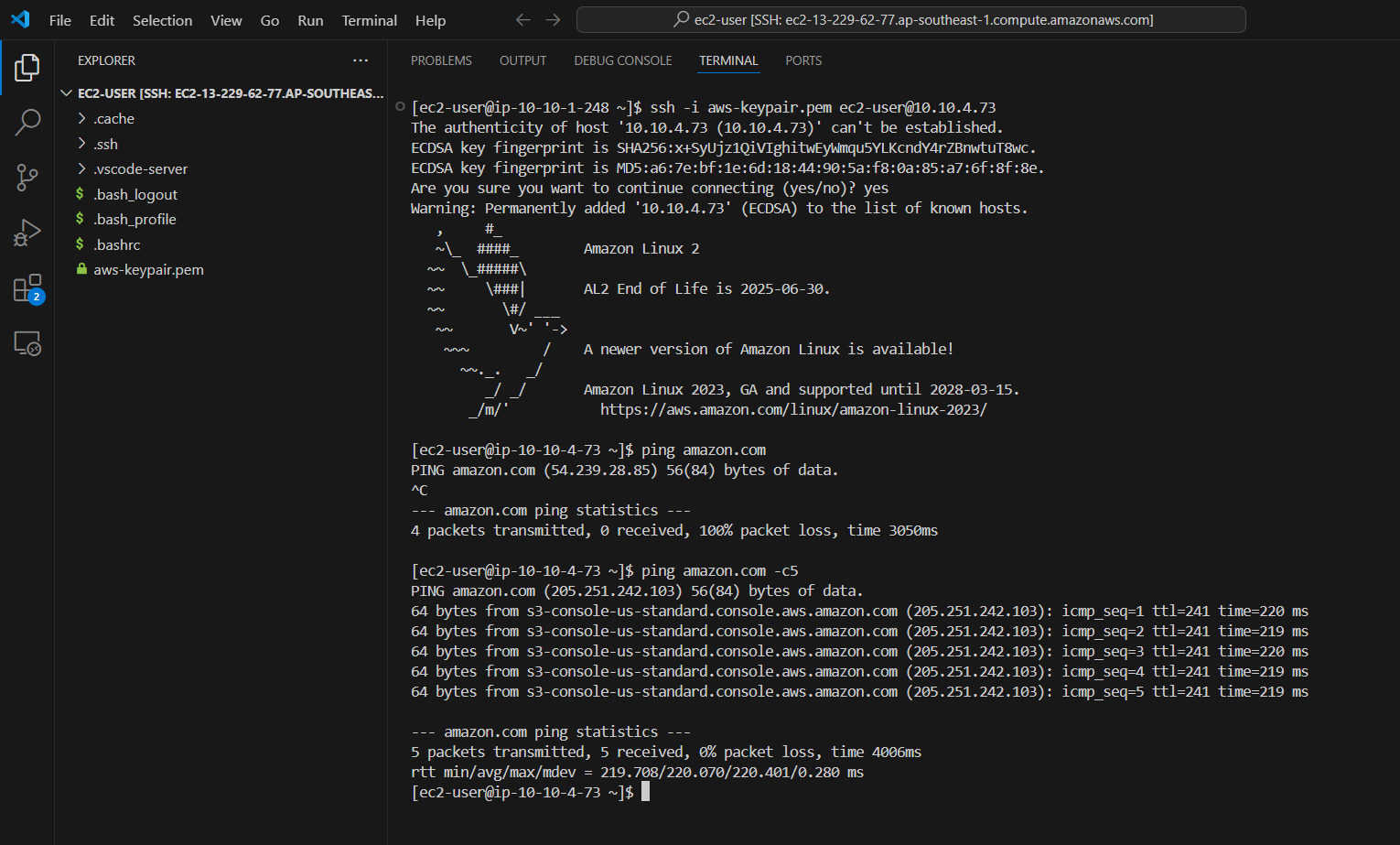
- Test ping
amazon.comsuccessfully from EC2 Private:
ping amazon.com -c5